
[SECURE_SESSION_ACTIVE]
PRATHAM VERMA _
Thinking like a hacker to build a stronger defense.

[SECURE_SESSION_ACTIVE]
Thinking like a hacker to build a stronger defense.
[SYSTEM_PROFILE_RETRIEVAL]

1+ years
Galgotias University
B.Tech Computer Science
2022-2026
60+ Projects
Security Analyst focused on Web, Mobile, and API security, I help organizations secure their most critical digital frontiers. Having conducted VAPT for 60+ client projects, I bring a hands-on, results-driven approach to vulnerability management.
I am also an active Public Speaker, having delivered 5+ sessions on emerging trends in Cybersecurity and AI Security. Whether through competing in hackathons or mentoring others through blogs. My approach combines offensive expertise with a commitment to continuous learning and community knowledge-sharing.

[ACCESS_LEVELS]
[LIVE_FREQUENCY]
Public Speaker dedicated to translating deep technical research into actionable defense strategies for the cybersecurity community.
[MILESTONES_LOGGED]

[CLASSIFIED_FILES]

ML-powered proxy WAF that distinguishes good vs. malicious requests. Intercepts incoming traffic and leverages machine learning for intelligent filtering.
Real-time secure messaging application with end-to-end encryption capabilities.

A deep learning project utilizing Transformer models to identify and block malicious phishing URLs in real-time.
[VERIFIED_CREDENTIALS]

[ENCRYPTED_STREAM]
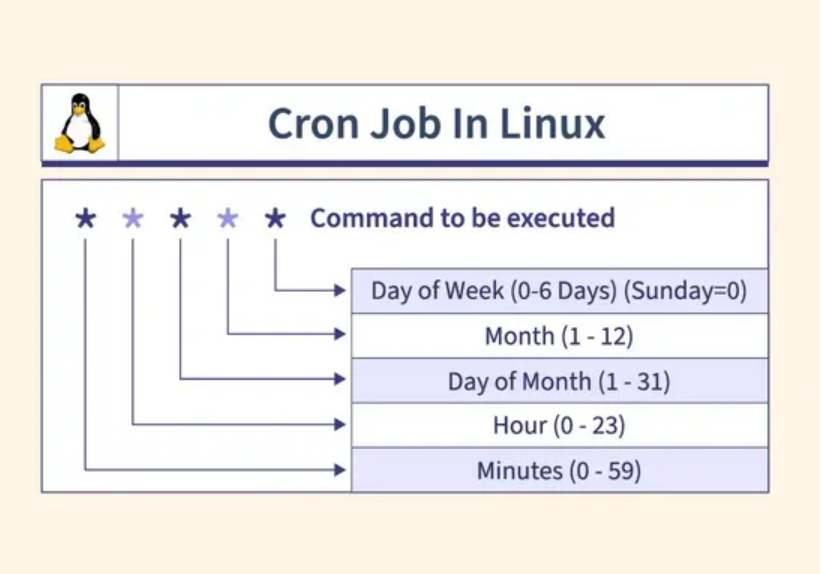
In the world of Linux Post-Exploitation, Cron Jobs are a goldmine.
Read More
iOS devices are renowned for their robust security. Apple's "walled garden" approach makes them a challenging target for penetration testers, but not an impenetrable one.
Read More
Clickjacking, also known as a "UI Redress Attack," is a malicious technique where an attacker tricks you into clicking on something different from what you perceive.
Read More
Verifying authenticity of messages and data in the digital age.
Read More
Transformative journey in problem-solving and code understanding.
Read More
Network protocol analyzer for capturing and analyzing packets.
Read More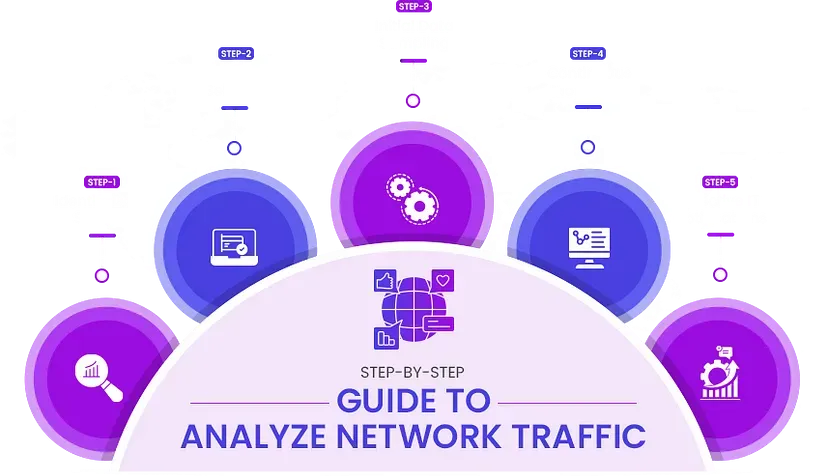
Essential security practices every developer should know.
Read More[SECURE_MESSAGE_UPLINK]